Update 10/11 – Exported TS, can download HERE. It is a bit more extensive than the one shown in Original post. This TS as several indirect contributes, I link back to their blogs, in both the posts and in the actual Description fields of the TS Steps.
- Includes Required packages, you’ll just have to modify them for your environment
- Bios Passwords (HP Bios Password File & Dell Bios Steps)
- Several Applications, I’ve left the steps, but just used a “Place Holder” App. You can replace them with the ones you’ve setup.
- Upgrade OS Windows 10 Anniversary Edition Step (Use your OS Upgrade Package)
- Install Dell Bios
- Install HP Bios
- Install RSAT
- Install Dell Command Update Package (You’ll need to download the software)
- Install Office 2016
- Install Updates Step, I’ve removed them and added “dummy” Install Software Update Steps as a reminder to replace them. There is a bug in 1606 when exporting that doesn’t like the Update Step. More info on Mike’s Blog
- Bitlocker – MBAM steps, you’ll need to modify these for your MBAM Server. – More Info HERE
—-
Original Post: 9/29
We’ve been working on our Windows 10 upgrade TS to move to Windows 10 1607, but we also want to use the same TS to upgrade Windows 7 and 8 computers when possible, and if we can upgrade in a way to leverage the additional Security features in Windows 10 that rely on Secure Boot (Credential Guard / Device Guard)
Requirements to upgrade Windows 7 and 8 computers to enable Credential Guard in 10, UEFI:
- Bios are already set to UEFI and Machines images in UEFI mode to have correct partitions already available.
- Windows 7, many of our systems are set to UEFI, with Secure Boot disabled.
- With HP, as long as you had it set to UEFI Hybrid (with CSM), during the TS, you can change it to UEFI Native. – On my oldest HP test model, When the bios is switching over to SecureBoot, it does prompt you to enter a 4 digit code to continue on some models. Once you enter it, the setup continues without problem.
- With Dell, as long as you had it set to UEFI, you can then enable Secure Boot during the TS
- Windows 8.1 could handle UEFI w/ SecureBoot, since we configured our Windows 8.1 machines this way already, it will be a pretty easy in place upgrade.
- Placement of your Bios Change Steps are important. You need to set it so it will change after the system is already upgrading into Windows 10, and no longer boots to Windows 7. (Make sure there are no reboots before you change the settings and you start the upgrade step.)
- Windows 7, many of our systems are set to UEFI, with Secure Boot disabled.
- If our Machines don’t already have the Bios set in this way to allow upgrading to Windows 10 to leverage the new features, we will do a Wipe & Reload instead of in-place upgrade to ensure we have UEFI & Secure Boot Enabled.
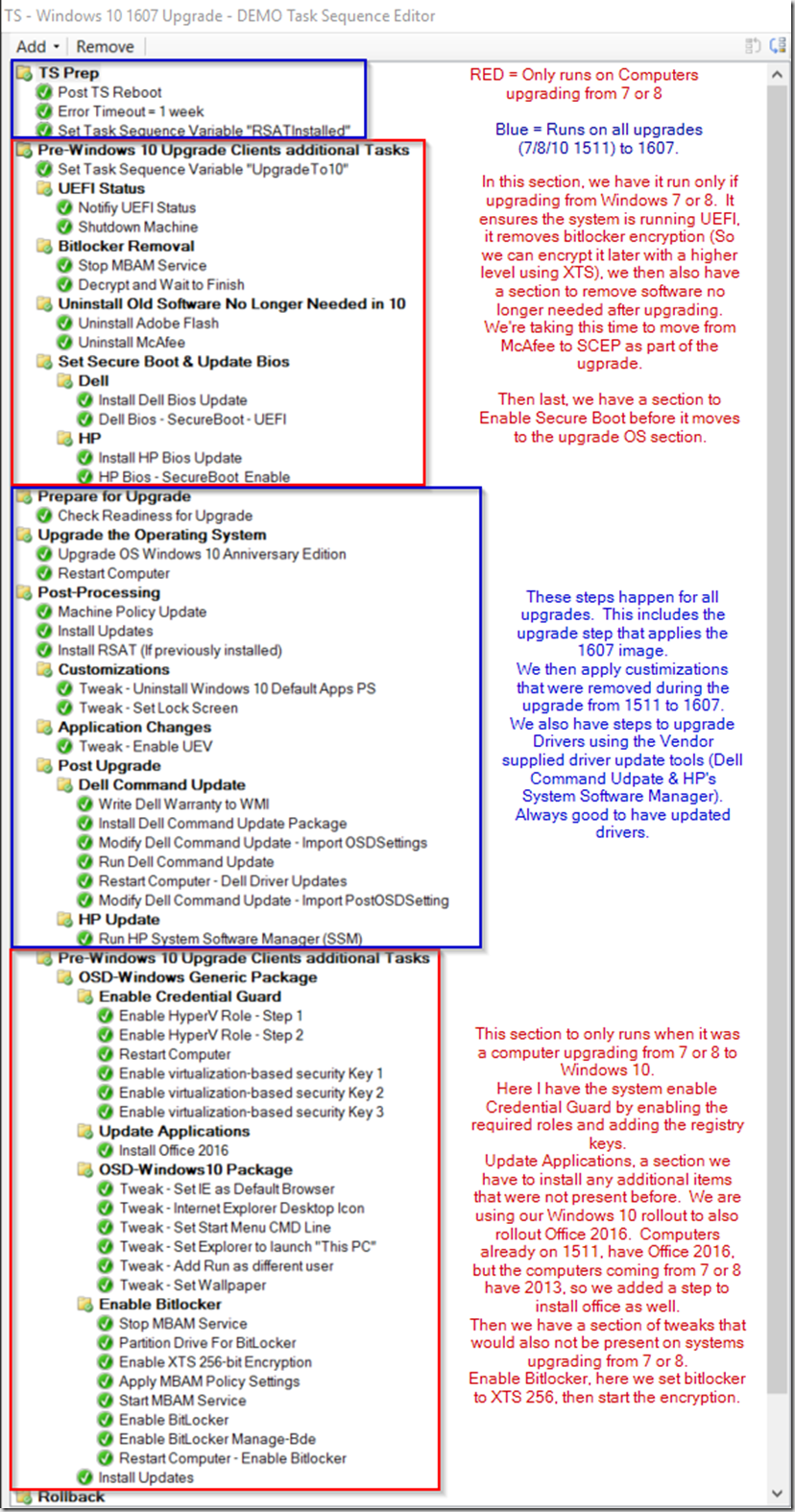
In the TS, we’ve added sections that only applies when upgrading from Windows 7 or 8, one before the upgrade and one after. In these steps, we do some cleanup of the systems before upgrade, as well as ensure they are already running UEFI. In the Post Upgrade, we run several other customizations as well as driver updates that we don’t need to if they were upgrading from 1511, which already had them included. Here is a Capture of the TS, I’ll then break it down.
First, we create a new Group for Machines that are currently on 7 or 8 that will be upgrading to 10
Set it to if None of these conditions apply, use the WMI Query: select * from win32_operatingsystem where caption like ‘Microsoft Windows 10%’![image[22] image[22]](https://garytown.com/wp-content/uploads/2016/09/image22_thumb.png)
- Now you need to create a Variable which will be used later:
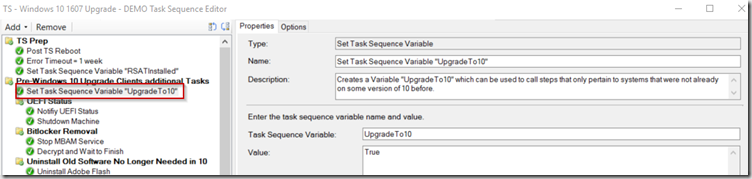
I created a variable called “UpgradeTo10” and set it to True. - UEFI Status – I have a section that will Check to make sure UEFI is set, otherwise it will fail and stop the TS. – Not necessary, but I just want to make sure we’re only upgrading systems that are set to UEFI so we can enable the additional security features Secure Boot offers.
Update 10/3/2016 – Blogged how I did this section HERE
- Bitlocker Removal – This decrypts the drive from AES-256, and waits for the decrypt to finish (So we can use the new Bitlocker Encryption available in 1511 & up). – Script to decrypt and wait until finished can be found here: http://www.tekuits.com/Blog/Post/12/Decrypt-Drive-and-Wait-for-Finish
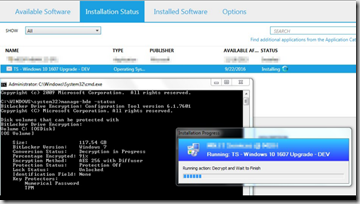
Note, we also disabled the MBAM service, we had MBAM kick in and start the encryption process during our testing. - Uninstall Old Software.. – This section I have it remove software we no longer want on the machines as we move to Windows 10, just a little Clean up.
- Set Secure Boot – This section loads the Bios Settings to Enable Secure Boot. If you have any reboots between these bios changes and the Upgrade OS step, it will prevent your computer from booting and stop the TS Process.
- Use the Vendor provided tools to create packages to modify your bios
After those steps, we have several steps that Pertain to the upgrade process in General, they happen no matter if the upgrade is from 7 or if upgrading from 1511 to 1607. We’ve found that upgrading from 1511 to 1607 removes some customizations, so we reapply them in that section, as well as run drivers updates using the Dell & HP Driver update tools. This saves us from having to add drivers to the OSD process, as they are updated dynamically.
Now we have another section that is just for the Computers upgrading from 7 / 8.1 to Windows 10. It consists of 4 sections, it runs when it sees the TS Variable “UpgradeTo10” is True.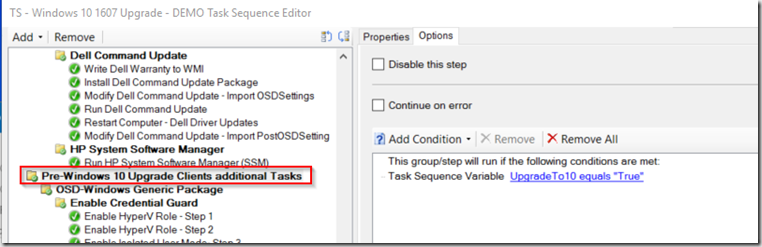
- Enable Credential Guard – This section contains several steps to enable the features in Windows 10 and apply the registry keys to enable – Steps are found on my post HERE. However, just change the DISM command from dism.exe /image:c: to Dism.exe /Online
- Step 1: cmd /c Dism.exe /Online /Enable-Feature /FeatureName:Microsoft-Hyper-V /All /NoRestart /quiet
- Step 2: cmd /c Dism.exe /Online /Enable-Feature /FeatureName:Microsoft-Hyper-V-Management-Clients /All /NoRestart /quiet
HERE is another nice post by @LofgrenPeter about enabling Credential Guard and removing the Hyper-V Tools if you don’t plan to use them.
- Update Applications – This section includes any other software we want to update to make it more in line with rest of our Windows 10 machines. In my example, all of our Current Windows 10 machines already have Office 2016, so when we upgrade Windows 7 machines, we want to upgrade Office from 2013 to 2016 as well.
- OSD-Windows10-Package – This sections has additional tweaks for Windows 10 that are not present when upgrading from 7 or 8.1, but were present already when upgrading from previous builds of Win10.
- Enable Bitlocker – This section sets the Registry Keys and Enables Bitlocker XTS-256 – Steps are found on my post HERE
Machines Tested: Windows 7 –> Windows 10 1607 – These systems updated in place without any user intervention, including the enabling of Secure boot, activating Credential guard and encrypting with XTS 256… unless otherwise noted.
- Dell (Bios already set to UEFI w/ Legacy Boot Rom enabled & SecureBoot Disabled before upgrade)
- Latitude E6430
- Latitude E6530
- Latitude E6440
- Latitude E6540
- Latitude E7240
- Latitude E7250
- Latitude E5550
- OptiPlex 7010
- HP (Bios already set to UEFI w/ Hybrid CSM & SecureBoot Disabled before upgrade)
- Revolve 810 G1 – During the first reboot in the “Upgrade OS..” Step, it prompts for user input to approve Bios Changes. I’ve found more info here, page 9.
- Revolve 810 G2
- Revolve 810 G3
Note, when you’re imaging Windows 7, make sure you’re imaging them in UEFI mode, to make upgrade easy. Dell should look like this, then choose the UEFI boot Flash Drive to start your image.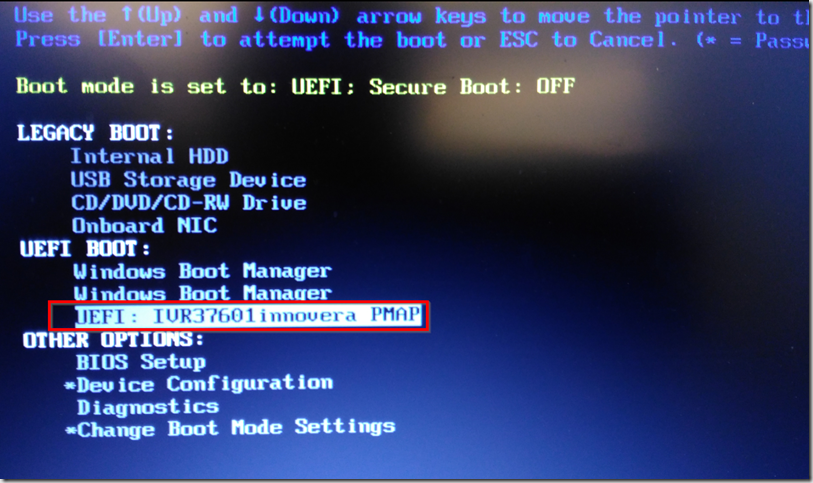
That will boot your computer in UEFI mode, format the Drive for UEFI and install Windows 7. Then when you go to upgrade to 10, there are no issues, you can have it disable legacy rom, and enable Secure Boot during the TS and have all the features Windows 10 has to offer without wipe and reload.
HP Bios should be set like this for your Windows 7 Deployments: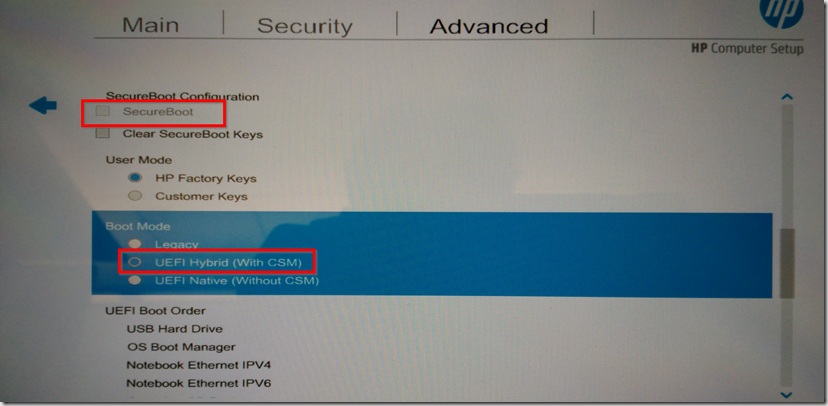
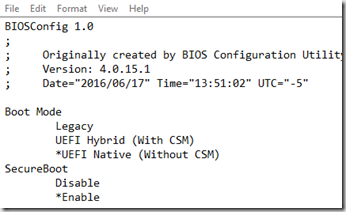
Then during the upgrade from 7 to 10, you can use the HP Bios Config tool (BiosConfigUtility64.exe) to change the settings:
CMD Step: BiosConfigUtility64.exe -set:EnableSecureBoot.txt -cspwdfile:HPBiosPassword.bin
Just have a packages with the HP Tools and your Password file in it.
For more info about adding drivers in a more traditional way for your upgrades, check out Johan’s Post: http://deploymentresearch.com/Research/Post/533/Improving-the-ConfigMgr-Inplace-Upgrade-Task-Sequence
Remember, this is NOT a solution to change Legacy Bios to UEFI, still recommend 1e’s solution for that. This was only if you had set your systems to UEFI while installing Windows 7 / 8. I did hear a rumor that the ConfigMgr team is working on a Bios->UEFI solution built into a future release… so that’s exciting.

Awesome blog post.
Is there any chance you would be willing to share this exported task sequence?
I’ll try to get to this next week. Glad you liked the post.
Love your post, it’s exactly what I have been looking for. If you don’t mind post an export version of your task sequence, I know you said you”ll get to it in week. Great job!
Try this: https://garytown.com/Downloads/TSExport.zip